Over the summer I stayed with a really close friend’s family in Dallas, and instead of buying the Mother flowers I decided to build her a wireless TOR router because she’s a bit of a conspiracy theorist (her family says that, not me), she uses a Ipad which doesn’t support TOR, and I really wanted to do something that was personal that had meaning and thought behind it. This router will allow her to browse the net anonymously (without big brother watching), I also fully encrypted the hard drive (in case they come after her), added libre office (open source microsoft office), and even changed the wallpaper to her daughter’s debutante photo (I’ll be hearing about this if she still reads my blog.) I hope that she actually uses it because it adds legitimacy to TOR because it’s for everyone (she is the sweetest lady, BTW) not just the intelligence community, criminals, and drug dealers.
It took me a while to gather the parts to put it together, as I went through a couple wifi adapters before I found one with the right chip set. Once you have the right parts, installation and setup are easy using this tutorial that I used. They used nano in the tutorials, but you can use any editor that you feel comfortable with. I used the following parts:
Setting the Pi as an access point
I used this tutorial. From the terminal run the following (I ssh’d into the pi from my mac) to install the software:
sudo apt-get install hostapd isc-dhcp-server
Then you need to edit the file for the DHCP server by running
sudo nano /etc/dhcp/dhcpd.conf
The change a couple lines by adding #, and then remove a # from a line so they look like this:
#option domain-name "example.org";
#option domain-name-servers ns1.example.org, ns2.example.org;
# If this DHCP server is the official DHCP server for the local
# network, the authoritative directive should be uncommented.
authoritative;
Then add this to the bottom:
subnet 192.168.42.0 netmask 255.255.255.0 {
range 192.168.42.10 192.168.42.50;
option broadcast-address 192.168.42.255;
option routers 192.168.42.1;
default-lease-time 600;
max-lease-time 7200;
option domain-name "local";
option domain-name-servers 8.8.8.8, 8.8.4.4;
}
Next, we change the interfaces by running
sudo nano /etc/default/isc-dhcp-server
changing the last line to look like this
INTERFACES="wlan0"
Then we set the wireless to have a static IP by running
sudo nano /etc/network/interfaces
making the file read like (change addresses where applicable, I did)
auto lo
iface lo inet loopback
iface eth0 inet dhcp
allow-hotplug wlan0
iface wlan0 inet static
address 192.168.42.1
netmask 255.255.255.0
#iface wlan0 inet manual
#wpa-roam /etc/wpa_supplicant/wpa_supplicant.conf
#iface default inet dhcp
up iptables-restore < /etc/iptables.ipv4.nat
Then tell the wireless adapter it’s address by running
sudo ifconfig wlan0 192.168.42.1
Configure the Access point by a using
sudo nano /etc/hostapd/hostapd.conf
put the following into the file
interface=wlan0
driver=rtl871xdrv
ssid=Pi_AP
hw_mode=g
channel=6
macaddr_acl=0
auth_algs=1
ignore_broadcast_ssid=0
wpa=2
wpa_passphrase=Raspberry
wpa_key_mgmt=WPA-PSK
wpa_pairwise=TKIP
rsn_pairwise=CCMP
be sure to [especially change the ssid (name of the router) and wpa-passphrase (password) and anything else that’s applicable to changes you made early or preferences.
We now need to add a line to file in the editor
sudo nano /etc/default/hostapd
pasting in the following
DAEMON_CONF="/etc/hostapd/hostapd.conf"
You now need to configure the network address by first changing another file
Run sudo nano /etc/sysctl.conf
adding
net.ipv4.ip_forward=1
then run the following to activate the file
sudo sh -c "echo 1 > /proc/sys/net/ipv4/ip_forward"
Finally, to make the ethernet (eth0) and wireless (wlan0) communicate, you need to run the follow commands
sudo iptables -t nat -A POSTROUTING -o eth0 -j MASQUERADE
sudo iptables -A FORWARD -i eth0 -o wlan0 -m state --state RELATED,ESTABLISHED -j ACCEPT
sudo iptables -A FORWARD -i wlan0 -o eth0 -j ACCEPT
so you don’t have to manually do it everytime you reboot, run
sudo sh -c "iptables-save > /etc/iptables.ipv4.nat"
Now all we need to do to get the access point working is running the hostapd software using the following commands
wget http://www.adafruit.com/downloads/adafruit_hostapd.zip
unzip adafruit_hostapd.zip
sudo mv /usr/sbin/hostapd /usr/sbin/hostapd.ORIG
sudo mv hostapd /usr/sbin
sudo chmod 755 /usr/sbin/hostapd
Your access point should now be working. To have all the software start on reboot run
sudo service hostapd start
sudo service isc-dhcp-server start
sudo update-rc.d hostapd enable
sudo update-rc.d isc-dhcp-server enable
Reboot you Pi by running
sudo reboot
Installing TOR
First install the TOR software using this code
sudo apt-get install tor
edit the config file by running
sudo nano /etc/tor/torrc
and paste in
Log notice file /var/log/tor/notices.log
VirtualAddrNetwork 10.192.0.0/10
AutomapHostsSuffixes .onion,.exit
AutomapHostsOnResolve 1
TransPort 9040
TransListenAddress 192.168.42.1
DNSPort 53
DNSListenAddress 192.168.42.1
Now we change our routing tables by running
sudo iptables -F
sudo iptables -t nat -F
Then we set-up for ssh routing in the future (I don’t want to give up a precious monitor)
sudo iptables -t nat -A PREROUTING -i wlan0 -p tcp --dport 22 -j REDIRECT --to-ports 22
now when you want to ssh into the pi you have to add a -p 22 to the command. Like this
ssh -l pi -p 22 192.168.1.100
Now do the other ports
sudo iptables -t nat -A PREROUTING -i wlan0 -p udp --dport 53 -j REDIRECT --to-ports 53
sudo iptables -t nat -A PREROUTING -i wlan0 -p tcp --syn -j REDIRECT --to-ports 9040
Now run the following to activate
sudo sh -c "iptables-save > /etc/iptables.ipv4.nat"
The following will create log files for debugging
sudo touch /var/log/tor/notices.log
sudo chown debian-tor /var/log/tor/notices.log
sudo chmod 644 /var/log/tor/notices.log
Finally, we start TOR manually running
sudo service tor start
Then make it start on every reboot
sudo update-rc.d tor enable
You’re done! You should now be able to connect to TOR wifi using the ssid and passphrase you used early.
The final product is about half the size of a normal router and looks like this:

*I was going to post a pic of the desktop (with the debutante photo) but I decided that I value my life… hahhahaha
QED
-update
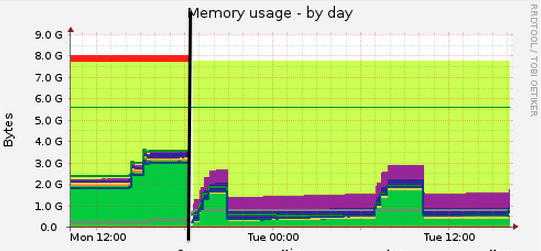
I did some speed testing on the router last night, and I discovered that you end up with about 25% of the speed that you would through regular wifi.